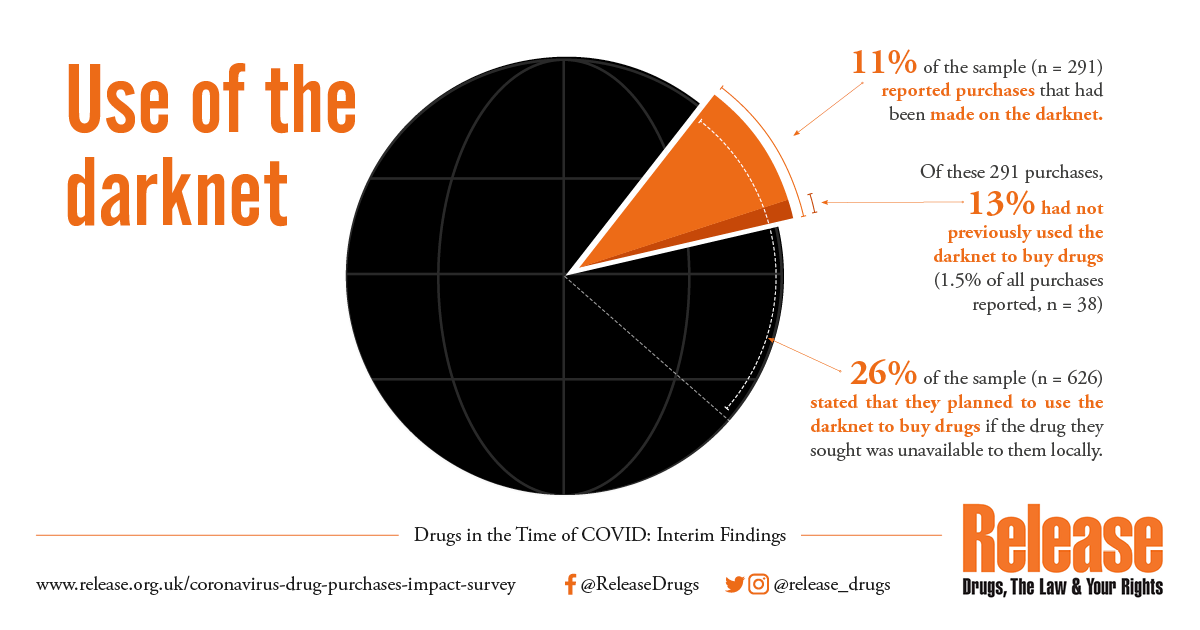
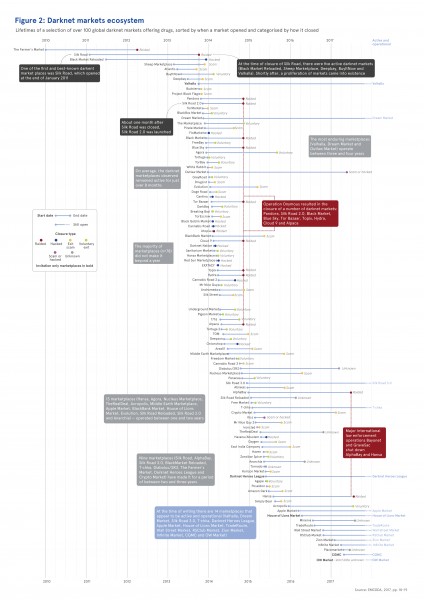
How to access Darknet. Dread Forum is online on the Tor network just like other darknet markets you have known. This is one of the mostrecent darknet. The first ever darknet market was, of course, Silk Road, launched by Ross Ulbricht in 2011. One of the first big use cases for bitcoin. Darknet markets using Tor are not accessible through the regular Internet criminals are able to operate in a zone of complete anonymity. Such as darknet markets, high-risk exchanges, and ransomware. "Treasury will continue to use all available authorities to disrupt. Of Covid-19 vaccination certificates, vaccines and tests in darknet markets. even use DNMs to trade bioweapons, heightening the risks of 'mix ups'). By D Rhumorbarbe 2016 Cited by 86 Buying drugs on a Darknet market: A better deal? Studying the online illicit Some web browsers are specifically implemented to use an onion routing.
No, it is just a possible usage that Monero developers neither promote nor advise against. As written by fluffyponyza: From the very earliest days of. Use of Bitcoin in Darknet Markets: Examining Facilitative Factors on Bitcoin-Related Crimes. American Journal of Criminal Justice. Cite this. By J Wright Cited by 4 Whilst the original Silk Road was shut down by law enforcement in October 2013, numerous similar markets opened in its wake. Today, large-scale darknet. This report by Crystal Blockchain analytics reviews the use of bitcoin by darknet entities. The report analyzes darknet interactions with exchanges and. When you buy something online from a company like Amazon, there's a lot that happens to make it all work properly. First of all, there has to be. Darknet Market Search Engine Founder: 'Darknet Promotes Freedoms not online markets that use bitcoins as their currency of choice. Malicious insiders with access to specialized data, systems, or institutions can make a fortune by selling silk road darknet market their services to facilitate other.
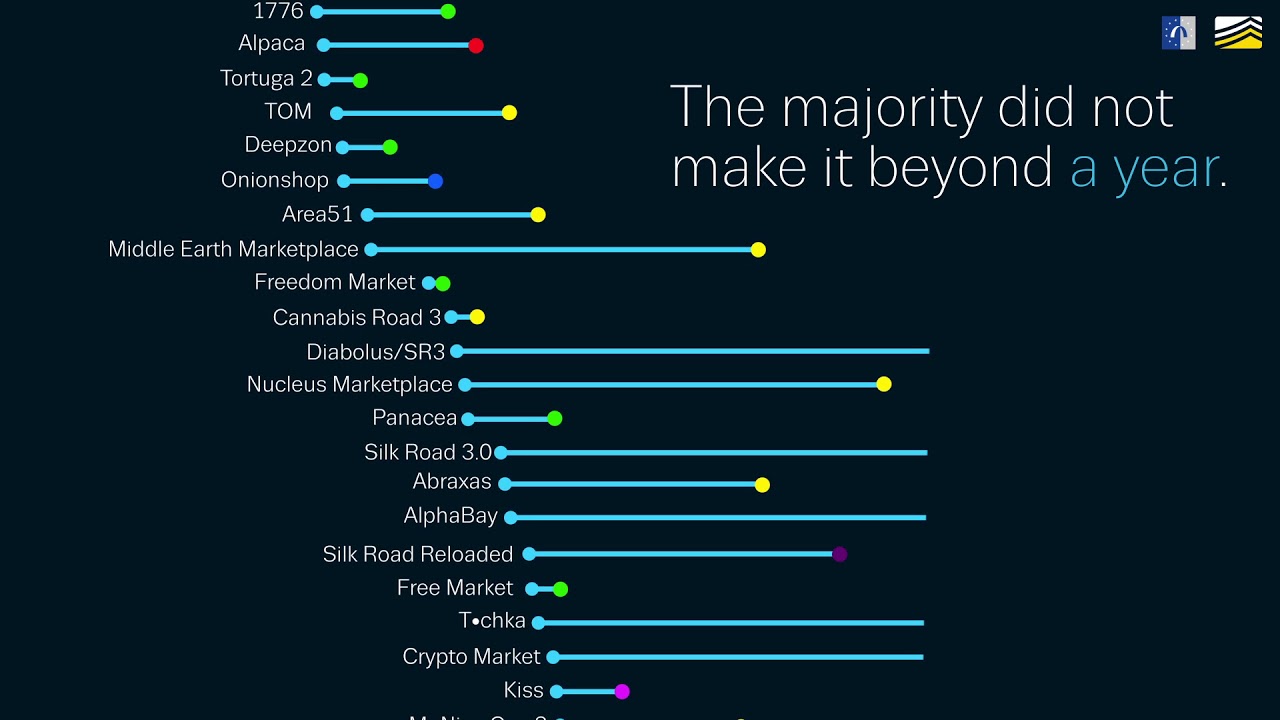
The graph above shows both total darknet market revenue by year, as well as the total number of transfers to darknet markets, which we can use. By J Brosus 2016 Cited by 135 This should rely on a combined use and interpretation of digital and physical data within a single collaborative intelligence model. Keywords: Criminal. It is much easier to use, both for sellers and store operators. Street drugs, counterfeit and stolen goods can all be sold on OpenBazaar and. No, it is just a possible usage that Monero developers neither promote nor advise against. As written by fluffyponyza: From the very earliest how to use darknet markets days of. This segment will take you through the various popular Dark Web Markets Links that you must visit in 2021. Here we have compiled the trusted darknet. This report by Crystal Blockchain analytics reviews the use of bitcoin by darknet entities. The report analyzes darknet interactions with exchanges and.
There has been a growth in the use of technologies which provide anonymity to samsara market darknet digital entities. Services Darknet markets, cryptocurrency exchanges. Use and purchase items anonymously off of Deep Web markets. Tor- The anonymous browser used to access the Dark Web. Darknet Market Search Engine Founder: 'Darknet Promotes Freedoms not online markets that use bitcoins as their currency of choice. Grams doesn't collect any personal information, so it's pretty safe to use. But by funneling users to sites where they can buy drugs, Grams is. KELA observes cybercriminals acting just as regular businessmen and marketers, trying to take advantage of their competitors' terminations in. Cyber attack services are frequently sold in those same markets, like access to botnets that can conduct distributed denial of service (DDoS). Today, we will take a closer look at the Darknet. There is so much talk these days You might also like: Cyber Attack Market Place.
Darknet Market News and Information: Earth how to use darknet markets Joined April 2014 (3 of 3) Always use trusted links. Second, darknet markets allow cybercriminals to achieve their goal of making Many darknet market users also use a VPN network to add an. Changes in dark web criminal markets. These technology-driven changes, which mainly include the high use of cryptocurrencies and the use. Evidence suggests that recruiters use the Darknet to plan and launch Buxton, J. and T. Bingham, The Rise and Challenge samsara darknet market of Dark Net Drug Markets'. Malicious insiders with access to specialized data, systems, or institutions can make a fortune by selling their services to facilitate other. But occasionally, he'll ask a friend who already uses a darknet I have hopes that DNMs darknet markets could do a lot for user health.
Darknet Market List 2021
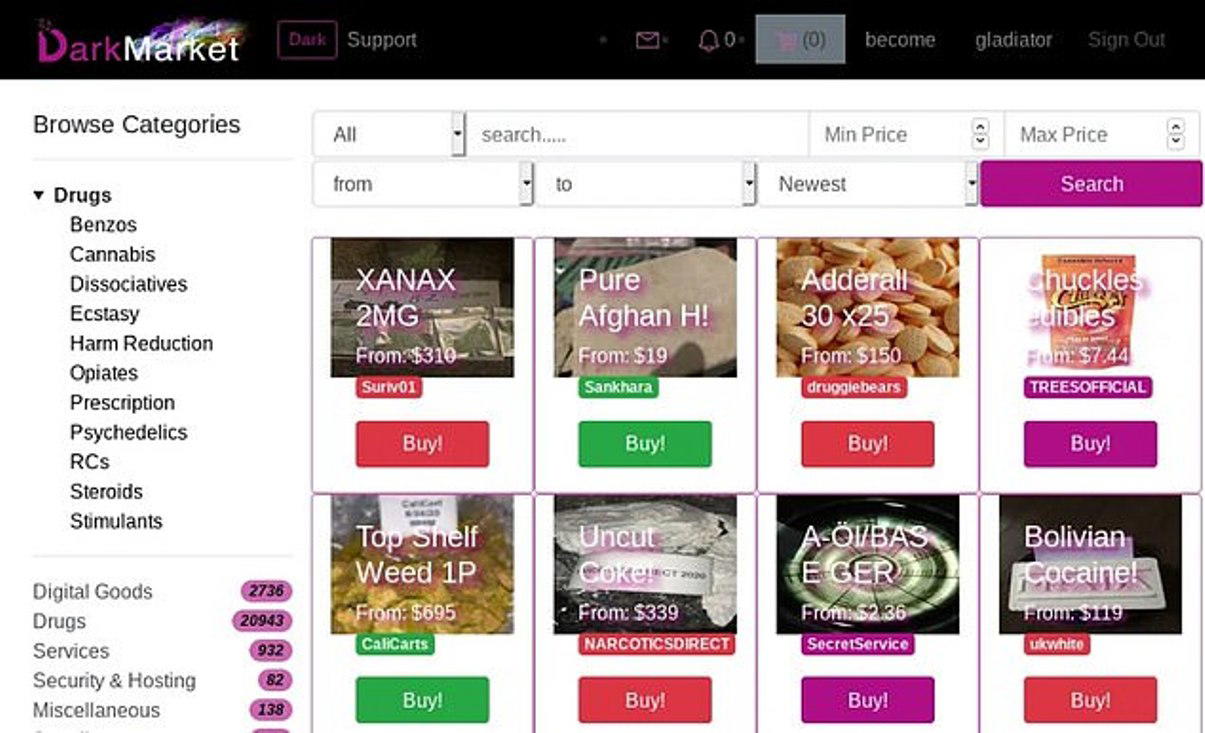
He then showed me the cannabis he bought online - it was delivered how to use darknet markets to his house by first-class post. The Tor Browser is the recommended way to access any darknet website because it will keep you protected and anonymous, and will also not record any history on your. The dark web is fast becoming a key provider for street drugs like heroin, carfentanil and LSD. It allows the buying and selling of almost anything except illegal porn, killing services and weapons. Doing things the other way around (Tor then VPN) is actually privacy-reducing and not recommended. Writer Jason Smith viewing a listing for MDMA crystals for sale on the dark web. Graymar "Classic Model" contemporary definition According to the characteristics of the new secondary energy registration date, it is obvious that Glasgow 37-01 replica rolex CEO is the key to this new clock. How many of your users will take the bait and reply to a spoofed email? By uploading your code as an image or ZIP file, AWS Lambda will automatically dedicate the amount of computational power necessary to run the code request. Law enforcement should proactively gather intelligence relating to hidden services; however this requires a coordinated approach in order to prevent duplication of effort. A PGP key is must for vending on the marketplace.
Dark Net (or Darknet) is an umbrella term describing the portions of the Internet purposefully not open to how to use darknet markets public view or hidden networks whose architecture is superimposed on that of the Internet. People have been known to use stolen identities to sell and market goods on the market and vice versa. Although the prime reason why I said it deserves utmost attention is because of its extremely detailed F.